Deep within the labyrinthine realms of cryptology lies Crown138, a/an/the legendary vault guarded by layers/obstructions/barriers of impenetrable enigma. Cracking/Unraveling/Breaking this cipher is no mere/a daunting/an epic feat, demanding/requiring/needing skill, knowledge/deduction, intuition.
But/However/ Yet, the allure of/to/for uncovering Crown138's secrets is irresistible/unyielding/alluring, drawing in aspiring/seasoned/dedicated cryptographers from across/throughout/far and wide the globe. With/Equipped with/Utilizing patience, persistence/determination/grit, and a touch/a sprinkle/a dash of ingenuity, these masterminds strive/endeavor/aspire to unlock the vault's treasures/secrets/mysteries.
- Perhaps/Maybe/Could it be? The answer lies within the intricate threads/web/structure of Crown138, waiting for a skilled/a discerning/an astute mind to untangle/decode/discern its hidden/veiled/masked truths.
Deep Dive into Crown138: A Hacker's Point of View
Stepping inside the world of Crown138 is like entering a labyrinth of complex code and hidden secrets. From the outside, it appears to be just another online platform, but for those who know how to look, there's a whole ecosystem waiting to be explored. A seasoned hacker would see this as a playground for their skills, a chance to push the boundaries of what's possible. They might concentrate on vulnerabilities within the platform's security, looking for cracks they can exploit. This isn't about causing harm, it's about understanding how things work, finding the blind spots, and ultimately making the system more robust.
- This is misconception that hackers are all about destruction.
- Some of them are ethical hackers, working to improve security by identifying vulnerabilities.
- The platform provide a sandbox for these skills.
But there's a darker side too. Malicious actors could exploit the same vulnerabilities for their own gain, stealing data or disrupting services. This is where the line between ethical hacking and cybercrime gets blurred. It all comes down to intent and actions.
Crown138: The Ultimate Capture-the-Flag Challenge
Prepare hackers worldwide for Crown138, the wicked Capture the Flag competition on earth. This year's event promises to push your limits with a mind-bending collection of challenges spanning web exploitation, and potentially some wild cards.
- Whether you're a seasoned veteran, Crown138 has something to offer.
- Participate in this digital showdown and prove you've got what it takes.
Don't miss out before it's too late! The clock is ticking.
Crown138: Confidentiality via Cipher
In the realm of modern cybersecurity, a paradigm shift has occurred. Traditional methods of safeguarding sensitive information are increasingly becoming vulnerable to sophisticated cyber threats. Introducing Crown138, a groundbreaking security protocol that leverages the timeless elegance of Enigma-style encryption to provide an unprecedented level of protection.
The core of architecture is built upon a complex network of algorithms that generate ever-evolving cryptographic keys, making it virtually impossible for adversaries to decipher the encoded data. Each transmission undergoes a rigorous process of transformation, rendering the information unintelligible to unauthorized parties.
- Crown138's's robust design thwarts even the most sophisticated cyberattacks, ensuring that your valuable assets remain securely safeguarded.
- Moreover, Crown138's user-friendly interface makes it accessible for individuals and organizations of all sizes.
Therefore, if you seek uncompromising security in an increasingly digital world, Crown138 stands as a beacon of trustworthiness.
Unveiling Crown138: A Journey into Cybersecurity
Diving deep into the complexities of Crown138 is akin to embarking on a thrilling expedition through the heart of cybersecurity. This intriguing threat actor has captivated the attention of security researchers and professionals worldwide with its ingenious tactics, leaving a trail of devastating breaches in its wake.
Understanding Crown138's methods requires analyzing the intricate web of its attacks. From invisible infiltration to the deployment of sophisticated malware, Crown138 exhibits a proficiency that poses a grave threat to individuals and organizations alike.
- Identifying the true motives behind Crown138's activities remains a critical challenge. Is it driven by nationalistic goals?
- Analyzing its digital footprints provides valuable information into the group's structure and potential collaborations.
As technology evolves, so too does the threat landscape. Keeping abreast of Crown138's latest tactics is crucial for safeguarding against future incidents.
The Crown138 Legacy: Shaping the Future of Hacking
The legendary Crown138 legacy continues to guide the future of hacking. This check here renowned group of security experts has crafted innovative methods that are now extensively utilized by hackers.
Their contributions in the field of cybersecurity have set the bar for ethical hacking. Crown138's uncompromising pursuit of knowledge has empowered a new generation of security professionals to push the boundaries of what is conceivable.
Their impact on the hacking community endures today, with their strategies serving as a foundation for future innovators.
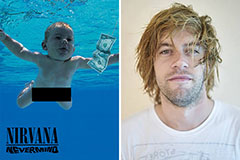 Spencer Elden Then & Now!
Spencer Elden Then & Now! Jenna Jameson Then & Now!
Jenna Jameson Then & Now! Ashley Johnson Then & Now!
Ashley Johnson Then & Now! Mike Vitar Then & Now!
Mike Vitar Then & Now! Katey Sagal Then & Now!
Katey Sagal Then & Now!